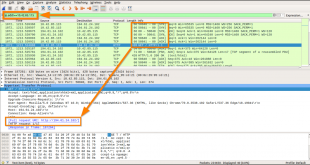
Learning Objectives Understand the advantages and goals of PCAP AnalysisHow to pivot into and away from PCAP Analysis (how to use findings for quicker analysis)Common tools to useHow data reduction aids in investigations Common Tools SnortTcpdumpWireSharkTShark Tools Covered Here SnortTcpdumpWireshark Notes Keep solid notes on your thinking around evidence and …
Read More »Incident Response without Windows Event Logs
This post discuss some Digital Forensics and Incident Response (DFIR) techniques you can leverage when you encounter an environment without Windows event logs. Where are the logs? at work, we regularly respond to security incidents with ineffective logging and auditing for the purposes of a cyber incident. In some cases, …
Read More »How to Allow Multiple RDP Sessions in Windows 10 and 11?
Remote users can connect to their Windows 10 and 11 computers via the Remote Desktop Services (RDP). It is enough to enable RDP in the device settings and connect to the computer using any Remote Desktop client. But there is a restriction on the number of simultaneous RDP sessions – …
Read More »How To Attack Kerberos
Kerberos Fundamentals Kerberos is a network authentication protocol that works on the principle of issuing tickets to nodes to allow access to services/resources based on privilege level. Kerberos is widely used throughout Active Directory and sometimes Linux but truthfully mainly Active Directory environments. TLDR: https://www.roguelynn.com/words/explain-like-im-5-kerberos/ I am aiming to approaching …
Read More »RDP Authentication Artifacts for DFIR Purpose
A good detection technique to spot Remote Desktop Connections that are exposed to the internet is to scan RDP event logs for any events where the source IP is a non-RFC 1918 address. This provides you a good way to check for locations that may be port forwarding RDP, like …
Read More »Windows Artifacts for Forensics Investigation
Generic Windows Artifacts Windows 10 Notifications In the path \Users\<username>\AppData\Local\Microsoft\Windows\Notifications you can find the database appdb.dat (before Windows anniversary) or wpndatabase.db (after Windows Anniversary). Inside this SQLite database you can find the Notification table with all the notifications (in xml format) that may contain interesting data. Timeline Timeline is a …
Read More »Windows Processes Investigation
smss.exe It’s called Session Manager. Session 0 starts csrss.exe and wininit.exe (OS services) while Session 1 starts csrss.exe and winlogon.exe (User session). However, you should see only one process of that binary without children in the processes tree. Also, more sessions apart from 0 and 1 may mean that RDP …
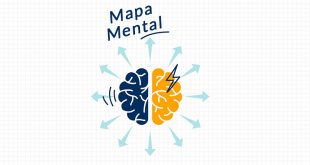
Read More »Active Directory Penetration Mind Map
click to see Full-Size Image Scan Network cme smb # enumerate smb hosts nmap -sP -p # ping scan nmap -PN -sV –top-ports 50 –open # quick scan nmap -PN –script smb-vuln* -p139,445 # search smb vuln nmap -PN -sC -sV # classic scan nmap -PN -sC -sV -p- # …
Read More »Check if your Active Directory passwords are compromised in a data breach
To compare Active Directory accounts against breached passwords you need access to your Active Directory with a specific privileged account, a password list with NTLM hashes and some PowerShell commands. But why should you do this? Password hashes of Domain accounts can be dumped locally from SAM, memory, remotely and …
Read More »Utilizing a Common Windows Binary to Escalate to System Privileges
Windows pwnage courtesy of trusted Windows binaries Introduction If you’ve ever tried to run a command prompt as administrator on your Windows OS before, you’ve seen a harmless popup appear. This is Windows User Account Control, or UAC. According to Microsoft, UAC “is a fundamental component of Microsoft’s overall security …
Read More »